Not in a default configuration. This is disabled for security reasons.
To enable this, first switch to SSL if you haven't already. To do so, go to System -> General Setup, and change webGUI protocol from HTTP to HTTPS.
Note
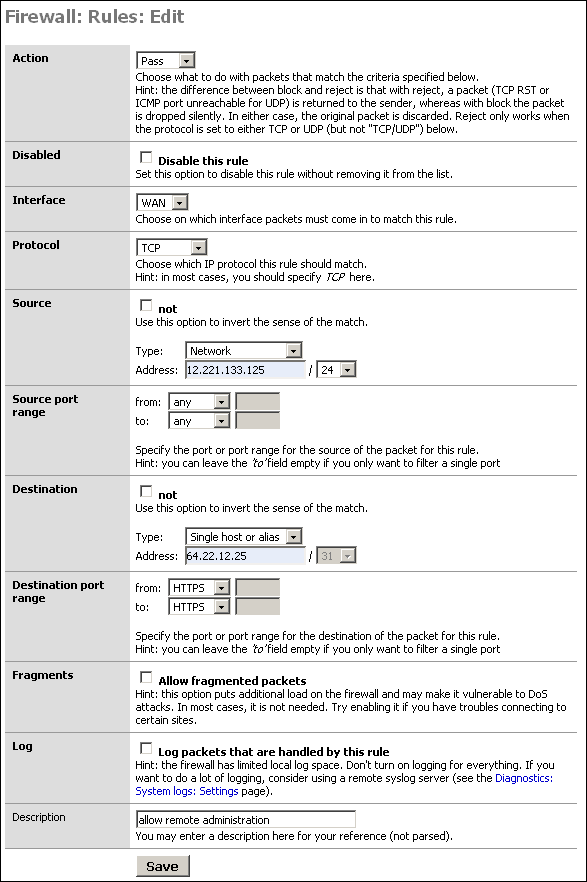
You may need to change the port number used by the webGUI. If you have used inbound NAT to open HTTPS to a web server, you'll have to change that port number to something other than the default 443, and change the destination port on the firewall rule shown below accordingly.
Now click Firewall -> Rules and click the ![]() on that screen. Add a rule like the following, replacing the made up IP
12.221.133.125 with the public IP of the remote system you wish to use to administer your
SmallWall, and 64.22.12.25 with the public IP of your SmallWall.
on that screen. Add a rule like the following, replacing the made up IP
12.221.133.125 with the public IP of the remote system you wish to use to administer your
SmallWall, and 64.22.12.25 with the public IP of your SmallWall.
This makes things a little trickier. You can't set the destination IP because it will change, and when it changes you would no longer be able to get to the webGUI. You can set the source to "any" rather than the WAN IP. Note that this will grant access to anything with an inbound NAT entry for the port (likely HTTPS), or anything behind a bridged interface with a public IP on that port. Unless you have multiple public IP's, this will not grant access to anything other than the webGUI. This does not grant that host access to HTTPS for anything on your LAN. Even if you do have multiple public IP's, opening HTTPS to a host you intend to allow to configure your firewall is likely of little to no concern.
Note
Opening your webGUI to the entire internet is a bad idea. Limit it to only the IP address required. If the remote administration host is on DHCP, you can limit it to the remote machine's ISP's netblock rather than opening it to the entire internet. Opening your firewall administration interface to the entire internet, even with strong authentication, is strongly discouraged on any firewall.
A much better option is to allow VPN access, and copnnect to the LAN side.